Choosing a VPN isn’t easy nowadays – what with all the hundreds of providers bombarding you with ads and promotions. It’s pretty hard to know which one actually secures your data, right?
No worries – here’s a simple guide that will show you how to pick a privacy-friendly VPN. You’ll learn what signs to look for, how to check if your VPN works with this leak testing tool, and which VPN providers are a safe choice.
Alright – Here’s How You Know a VPN Takes Your Privacy Seriously
To really protect your privacy on the web, the VPN needs to offer the following things:
1. A No-Logs Policy
Okay, so a VPN stops your ISP from spying on what you do online? But how does that help you if the VPN will spy on your traffic instead?
Yep, that’s what can happen if your VPN keeps usage logs. Basically, it’s data about what websites you browse while using a VPN.
And even connection logs aren’t privacy-friendly. They don’t store browsing data, but they can still include your IP address. And that can reveal a lot of information:
- What country and city you live in
- What your ZIP code is
- Who your ISP is
That’s why a zero-log policy is a must. That way, even if VPN servers get hacked or seized, no user data will be at risk.
Ideally, the provider should have independent audits or legal proof to verify their claims.
2. Military-Grade Security
A VPN can’t protect your privacy if it offers poor security. By that, I mean stuff like limiting or encouraging access to PPTP and L2TP/IPsec, or using outdated encryption ciphers like Blowfish.
It’s best if you see stuff like AES encryption (the NSA actually uses it for Top Secret-level information), and encryption keys that are either 128 bits or 256 bits. Also, the VPN should offer protocols like OpenVPN, IKEv2, and SoftEther. SSTP is also secure, but keep in mind it’s solely owned by Microsoft – a company that shared data with the NSA.
3. A Kill Switch
Sometimes, your VPN connection might just go down. It can happen due to many reasons:
- The distance between your device and the VPN server is too big.
- The VPN protocol you’re using is too resource-intensive.
- The VPN client suffers crashes.
Whichever the case, one thing will happen – your traffic will be exposed until the VPN connection is up and running again. And during that time, anyone can spy on it – your ISP, the government, advertisers, and hackers.
Well, a Kill Switch keeps you safe from that. Basically, it shuts off your web access when your VPN connection goes down. Your Internet will only work once the VPN connection is stable again.
4. Leak Protection
A VPN can use all the high-end features it wants to protect your privacy on the web. But if it suffers any leaks, it’ll be completely pointless.
By leaks, here’s what I mean:
- DNS leaks – This is when the VPN doesn’t route your website connection requests through their DNS server. Instead, they go through your ISP’s server, meaning they can see what you’re browsing.
- IP leaks – These happen when the VPN doesn’t route your IP address through the encrypted tunnel, leaving it exposed. They can be IPv4 leaks that happen due to communication errors or poor VPN configuration, or IPv6 leaks which occur because the VPN doesn’t support or block IPv6 traffic.
- WebRTC leaks – This occurs when the WebRTC functionality within browsers takes priority over the VPN tunnel, causing IP leaks.
Now, most reliable VPNs will at least have DNS and IP leak protection. Some might even have WebRTC leak protection in the form of browser extensions that block it.
But if there’s no mention of any kind of leak protection, that’s a huge problem for your privacy.
5. Limited Data Collection
This isn’t the same as a no-log policy. By this, I mean the VPN provider shouldn’t ask you for a lot of personal information when you sign up. Ideally, none at all.
At most, the VPN should only need your email address. And it should support anonymous ones like ProtonMail or Tutanota. If they ask you for stuff like your real name or phone number, that’s a red flag.
6. Cryptocurrency Payments
Unlike credit card or PayPal payments, cryptocurrency payments can’t be traced back to you so easily. And they don’t reveal any information to the VPN provider – just your crypto wallet address.
Of course, cryptocurrencies aren’t completely anonymous if you use platforms like Binance or Coinbase, since they require you to give photos of your ID and/or your phone number. But luckily there are ways to buy Bitcoin anonymously to a certain extent.
One Simple Way to Make Sure the VPN Is 100% Legit
While all those features are a good sign the VPN takes your privacy seriously, you need to be sure too. So, you should check if your VPN works with this leak testing tool from ProPrivacy – ideally during the free trial or money-back guarantee period.
The tool is very easy to use, delivers results in seconds, and will check for multiple issues: IPv4, IPv6, DNS, and WebRTC leaks.
This is what you’ll want to see:
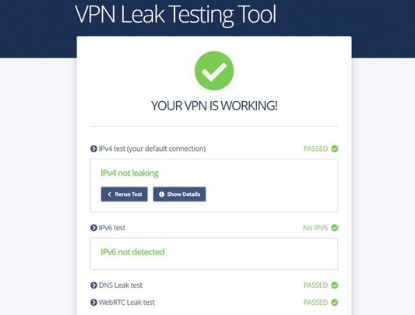
If you detect any issues, ProPrivacy has a link to a helpful guide on how to deal with them. If the leaks are the VPN’s fault, you should consider switching to a different one, though.
What VPNs Can You Trust With Your Privacy?
Some really good VPNs that meet all the criteria I mentioned, and also passed the VPN leak tests include NordVPN, ExpressVPN, CyberGhost, and Ivacy.
If you know other decent VPNs people can trust with their privacy, let us know in the comments below. Also, feel free to share any other privacy-oriented features people should check out when comparing VPN services.








 Agree (0)
Agree (0) Disagree (
Disagree (







__small.png)










